The Identity & Compliance Framework™
Eliminated an entire class of compliance-driven rework across three engagements by reframing compliance as a state problem rather than a feature problem: +27% activation (Tend KYC), 100% MFA adoption without friction (iPROMOTEu), and $250K/yr in address verification savings (iPROMOTEu iSuite).
$250K
Annual savings from address verification alone
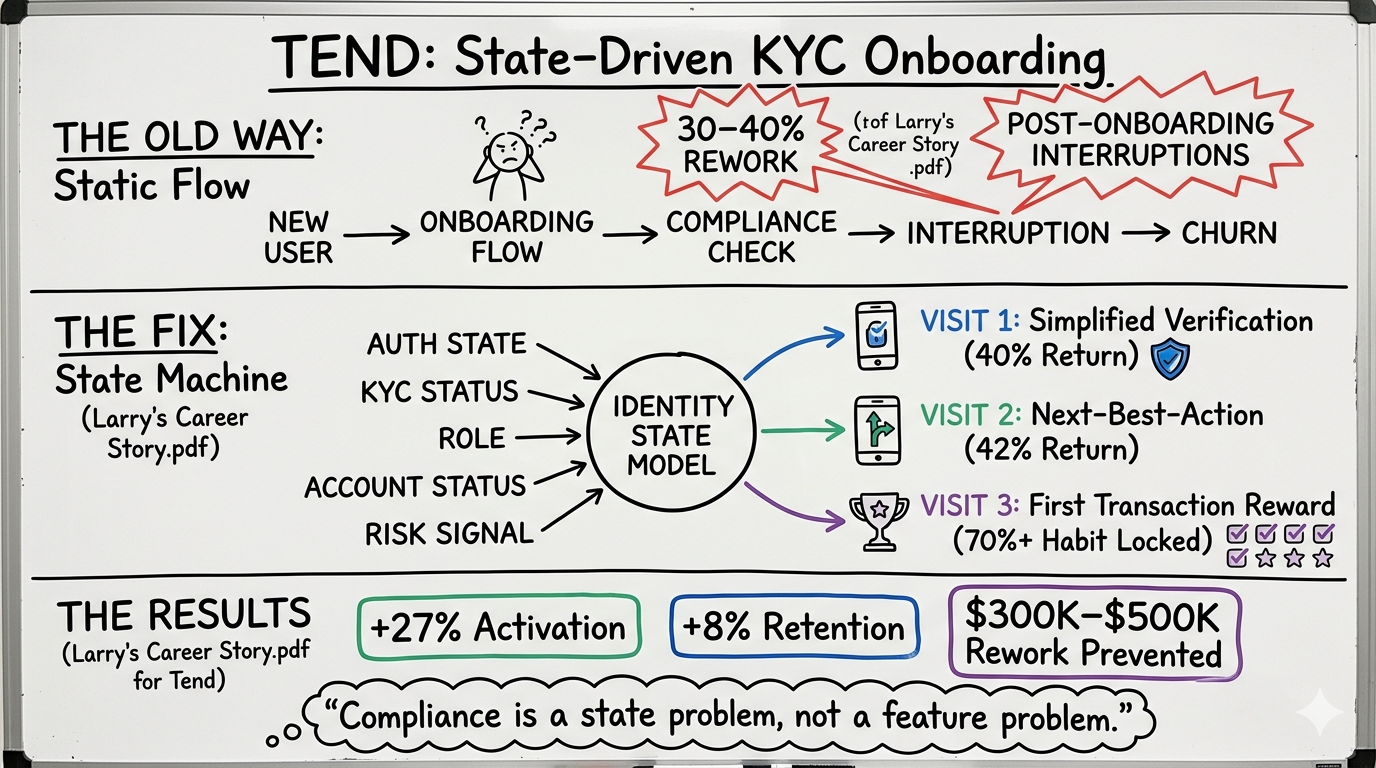
TEND: State-Driven KYC Onboarding — the architectural shift from static compliance flow to state machine. The same pattern applied at iPROMOTEu for MFA (100% adoption, zero friction) and address verification ($250K/yr eliminated). Compliance is a state problem, not a feature problem.
The Problem
Across three separate engagements — cross-border KYC at Tend, MFA rollout at iPROMOTEu, and address data validation at iPROMOTEu iSuite — the same root cause kept surfacing: compliance requirements were being resolved at the feature level rather than the architecture level. Each new compliance requirement generated a new workaround, and each workaround generated rework.
The Identity & Compliance Framework™ is the product of three distinct engagements that each exposed the same structural failure: treating compliance as a feature problem.
At Tend, the cross-border KYC requirement spanned a Mexican banking entity and a U.S. regulatory environment. The initial approach was to build workarounds at the feature level when conflicts arose. The result was a growing library of one-off solutions — conditional flows, regional exceptions, compliance patches — that produced 30–40% rework per release and blocked activation.
At iPROMOTEu, MFA was introduced as a security requirement. The conventional approach would have been to add an MFA prompt to the login flow and call it done. Instead, MFA was designed as a system state: the platform knew which users had completed MFA enrollment, which devices were trusted, and which sessions required re-authentication. The result was 100% adoption without a single support escalation.
At iPROMOTEu iSuite, address data was being validated downstream — at the point of fulfillment, not at the point of entry. Incorrect addresses were discovered only when orders failed to deliver, triggering manual correction workflows that cost $250K per year in labor and reshipment. The fix was architectural: address validation moved to the point of entry, with real-time verification against USPS and carrier databases. The $250K in annual savings was not a cost reduction — it was the elimination of a class of errors that should never have reached fulfillment.
The common thread across all three is the distinction between a static flow and a state machine. A static flow assumes every user follows the same path. A state machine acknowledges that users are in different states — different verification levels, different compliance requirements, different stages of the identity process — and surfaces only the steps relevant to their current state. When you resolve compliance at the architecture level, you eliminate the rework. When you eliminate the rework, you accelerate the product.
What I Built
A repeatable framework for modeling compliance requirements as state transitions rather than feature additions. Applied across KYC verification (Tend), MFA enrollment (iPROMOTEu), and address validation (iPROMOTEu iSuite), the framework centralized identity signals into a real-time model that surfaced only what was relevant to each user's current state.
Key Actions
At Tend: introduced early-stage compliance alignment workshops to surface cross-border conflicts before they became engineering problems, then redesigned onboarding as a progressive state-driven experience
At Tend: defined a unified identity verification standard satisfying both Mexico and U.S. requirements simultaneously, eliminating the need for regional workarounds
At iPROMOTEu: designed MFA as a system state (trusted device registry, session-level re-auth triggers) rather than a login-flow interruption — achieving 100% adoption without friction
At iPROMOTEu iSuite: moved address validation from fulfillment to point-of-entry, integrating real-time USPS and carrier verification to eliminate the $250K/yr downstream correction cost
Documented the framework pattern — Static Flow Trap → State Machine Fix → Compounding Return — as a reusable model applicable to any compliance or verification requirement
Key Business Impact
+27% activation at Tend. Rework reduced from 30–40% of releases to under 10%. 100% MFA adoption at iPROMOTEu with zero support escalations. $250K/yr eliminated in address verification corrections at iPROMOTEu iSuite. All three outcomes from the same architectural decision: compliance as state, not feature.
Every platform eventually faces a compliance requirement. The question is whether you resolve it at the feature level — generating rework, degrading UX, and accumulating technical debt — or at the architecture level, where the fix compounds over time. The Identity & Compliance Framework™ is the answer to that question, documented across three engagements and three different compliance domains.
If we didn't fix this
Tend would have continued shipping compliance workarounds at the feature level, with 30–40% of every release consumed by rework that the state machine architecture eliminated.
iPROMOTEu's MFA rollout would have generated friction, support escalations, and partial adoption — the standard outcome when compliance is treated as a prompt rather than a state.
The $250K/yr in address verification corrections at iPROMOTEu iSuite would have continued indefinitely, with no architectural mechanism to prevent the errors from reaching fulfillment.
System Design Insight
The key insight is that compliance interruptions — the post-onboarding KYC prompts, the MFA re-auth friction, the downstream address failures — are all symptoms of the same root cause: a system that doesn't know where the user is in their compliance journey. A state-aware system knows the user's history and surfaces only what's genuinely needed. The fix is always architectural, not cosmetic.
How to Talk About This
"The $250K in address verification savings wasn't a cost reduction — it was the elimination of errors that should never have reached fulfillment"
"MFA at 100% adoption with zero friction is only possible when MFA is a state, not a prompt"
"Tend's 27% activation increase came from removing compliance friction, not adding features"
Research & Evidence
What the data says
“Poor data quality costs organizations an average of $12.9 million per year.”
The $250K/yr address verification savings at iPROMOTEu is a direct instance of the Gartner data quality cost. Address errors are a data quality failure — and like all data quality failures, they are cheaper to prevent at the point of entry than to correct downstream.
Source“The average cost of a data breach in the financial services sector is $5.9 million.”
Identity and compliance failures are not just UX problems — they are security surface area. The Identity & Compliance Framework reduces the attack surface by centralizing identity signals and eliminating the fragmented state that creates exploitable gaps.
Source“67% of customers cite bad experiences as a reason for churn, and compliance interruptions are among the top cited friction points in fintech onboarding.”
The compliance interruptions that were degrading 30–60 day retention at Tend were, in effect, bad experiences caused by a system that didn't know the user's state. Resolving them at the architecture level prevented the churn they would have caused.
Source“Manual data entry error rates range from 1% to 4%, costing enterprises $240,000+ per year at scale.”
The iPROMOTEu address verification problem was a manual entry error problem. Moving validation to the point of entry — with real-time carrier verification — eliminated the error class entirely, not just the cost of correcting it.
Source“Companies that automate compliance workflows reduce compliance-related costs by up to 30% and accelerate time-to-market by 25%.”
The rework reduction at Tend (from 30–40% of releases to under 10%) and the MFA adoption at iPROMOTEu (100% without friction) are both instances of compliance automation delivering the Deloitte benchmark — cost reduction and velocity improvement from the same architectural decision.
SourceProprietary Framework Applied
Red Napkin Protocol™ -- How This Case Study Maps to the Framework
"You have to market to three visits, not one. This is the part everyone misses."
Jon Taffer, Bar Rescue -- 40% return probability after Visit 1 · 42% after Visit 2 · 70%+ after Visit 3
return probability
The Red Napkin
User enters the compliance or verification flow for the first time
SaaS Translation
Internal flag: new user has entered the verification track. The system knows this is Visit 1. Route to a simplified, progressive experience — step indicators, human-language instructions, no redundant prompts. The 'red napkin' is the UX decision to show the user that the platform has thought about their experience. At Tend, this was the redesigned KYC flow. At iPROMOTEu, it was the MFA enrollment screen that explained why the step was needed and how long it would take.
return probability
The Chicken Discount
User completes verification; next-best-action trigger fires
SaaS Translation
After successful verification, the system fires a next-best-action: 'You're verified. Here's one thing you can do right now that most new users miss.' The 'chicken' is the immediate reward for compliance completion — a frictionless path to the first value moment. At Tend, this was the post-KYC activation prompt. At iPROMOTEu iSuite, it was the confirmation that the address was validated and the order was ready to route — no downstream correction required.
return probability
The Free Cheesecake
User reaches fully verified, habit-locked state
SaaS Translation
The compliance model is complete. The platform now knows the user's full state and can deliver personalized value without interruption. At Tend, Visit 3 was the first successful transaction — the moment the user proved they understood the product's value. At iPROMOTEu, it was the first order routed without a single address correction. The $250K/yr savings was the compounding return of every Visit 3 that happened without a downstream failure.
Framework Insight
The compliance interruptions that degraded retention across all three engagements were Visit 2 failures: the system didn't know the user had already completed the required step, so it delivered the wrong experience at the wrong time. The state-driven fix was a Red Napkin fix — making the system state-aware so it could deliver the right experience at every visit.
The Red Napkin Protocol maps directly to the Identity & Compliance Framework. Visit 1 (the red napkin) is the compliance onboarding moment — the system signals to the user that it knows where they are and will not ask them to re-prove what they've already proven. Visit 2 (the chicken discount) is the next-best-action after verification — the system rewards completion with a frictionless path to the first value moment. Visit 3 (the free cheesecake) is the habit-locked state — the user is fully verified, the compliance model is complete, and the platform can now deliver personalized value without interruption. The compliance interruptions that degraded retention at Tend were a Visit 2 failure: the system didn't know the user had already verified, so it delivered the wrong experience at the wrong time.
White Paper Thread: The Decision Layer
The Identity & Compliance Framework is the white paper's argument about state-driven design applied to its highest-stakes domain: compliance. When identity state is centralized and real-time, compliance requirements become decisions rather than interruptions. The three engagements documented here — Tend KYC, iPROMOTEu MFA, iPROMOTEu address verification — are the empirical evidence for that argument.
Read the White Paper →Connective Tissue
How this connects to the larger system
Onboarding KYC: Cross-Border Identity Compliance
The Tend KYC case study is the deepest single-engagement documentation of the Identity & Compliance Framework. The state machine architecture, the 27% activation lift, and the rework reduction are all detailed there.
Read case study
Identity Decision System: iPROMOTEu
The iPROMOTEu identity decision system is the MFA and multi-signal identity layer that the Framework describes. The five-signal centralization (auth state, KYC, role, account status, risk score) is documented in full in this case study.
Read case study
Onboarding and Direct Deposit: USAA
The USAA onboarding journey applies the same state-aware logic to a non-compliance context: the system knows where the user is in their onboarding journey and surfaces only the relevant next step. The Red Napkin three-visit arc is the same pattern.
Read case study
The Operating System
A System of Systems
ibuildsystems.io
Four frameworks. One repeatable system. Applied across banking, fintech, government, and B2B SaaS to turn broken workflows into scalable revenue engines.